Mike Turicchi
Recent Posts
This video describes the benefits of Aruba Network-as-a-Service. Please contact NCS Technologies, Inc. for more information about Aruba Network-as-a-Service.
Read More
0 Comments Click here to read/write comments
Giving your teams and business a competitive edge
Posted by Mike Turicchi on Nov 13, 2023 2:54:00 PM
It's proven that companies that provide employees with the best tools to help them do their best work generally beat the competition. If your organization is working to better equip teams, take a look at this eBook about the advantages of the HP Elite Dragonfly series.
Read More
0 Comments Click here to read/write comments
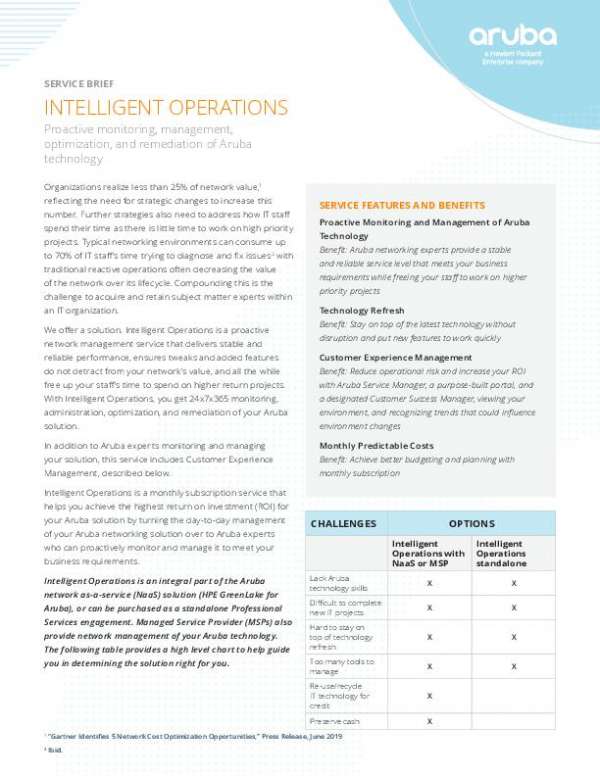
This solution brief describes the features of Aruba Intelligent Operations, a proactive network management service that delivers stable and reliable performance. Please contact NCS Technologies, Inc. for more information about Aruba Intelligent Operations.
Read More
0 Comments Click here to read/write comments
Business planning has changed greatly over the past few years, with most ten-year plans thrown out the window as the pandemic changed everyone's operations. Download this thought-provoking eBook showing how successful organizations are moving forward to the future where the view of work is always changing.
Read More
0 Comments Click here to read/write comments
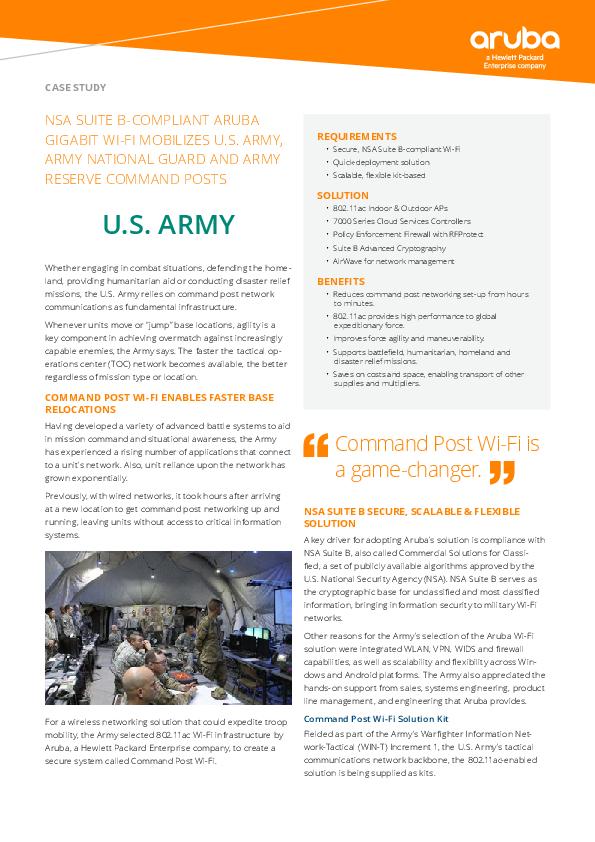
NSA Suite B-Compliant Aruba Gigabit Wi-Fi Mobilizes U.S. Army, Army National Guard, and Army Reserve Command Posts
Posted by Mike Turicchi on Nov 6, 2023 10:42:06 PM
This case study describes how the Aruba NSA Suite B provides the military with a secure, scalable, and flexible solution that can be deployed in minutes. Please contact NCS Technologies, Inc. for more information about the Aruba NSA Suite B.
Read More
0 Comments Click here to read/write comments
Enable State and Local Government to Modernize Network Infrastructure from Edge to Cloud
Posted by Mike Turicchi on Nov 6, 2023 11:42:56 AM
This solution brief examines the benefits of adopting an advanced Aruba SD-WAN platform for state governments. Please contact NCS Technologies, Inc. for more information about Aruba SD-WAN platforms.
Read More
0 Comments Click here to read/write comments
What are the current trends in hybrid and remote work? If this question is on your mind, check out this blog post from Forbes Advisor showing the most recent remote work statistics that are shaping the professional world and working environments across the nation.
Read More
0 Comments Click here to read/write comments
In this video, you'll learn about the top priorities for technology in government, and you'll see how Aruba delivers on those priorities. To learn more, please contact NCS Technologies, Inc. for further details.
Read More
0 Comments Click here to read/write comments
In this video, you will see the ways technological needs are evolving for government and constituents—plus how Aruba can help with this transformation. If you would like to learn more, please reach out to NCS Technologies, Inc..
Read More
0 Comments Click here to read/write comments
Share this image to let your customers know you'd like to talk with them about the possibilities of their Office, modernized.
Read More
0 Comments Click here to read/write comments